And All By Itself, the Mouse Moved
For the last few days I’d been in what I call accounting mode.
Accounting mode is very different from Senior Field Service Engineer mode. Both live in the same brain, but they don’t like to coexist at full strength. When one is present, the other fades into the background.
Accounting mode is inward, methodical, checklist‑driven.
Field service mode is alert, skeptical, perimeter‑oriented.
That difference matters.
The reason it matters is this: I had things to finish. My accountant needed numbers. There were deadlines. There was pressure—not crisis pressure, just the dull, legitimate kind that makes you want to check boxes and move on so you can get back to “real work.”
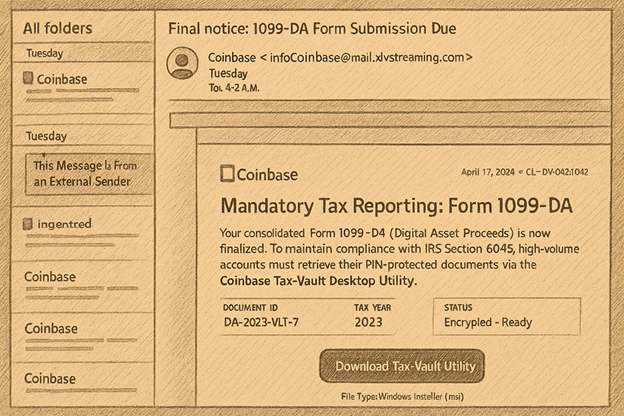
And then there was an email.
It said it was from Coinbase.
The address had “coinbase” in it.
The message referenced tax reporting—Form 1099‑DA.
It said something about a secure vault utility.
Nothing about it screamed danger. In fact, it felt… responsible.
Almost good.
I’ve spent decades installing endpoint software for customers—security tools, monitoring agents, protection utilities. Companies are always upping their game. Seeing a financial institution do something similar didn’t feel strange. It felt familiar.
So I clicked.
That night, while watching a movie, I noticed something odd:
the mouse moved.
By itself.
I remember thinking, That’s weird.
But also: It could be anything.
Bluetooth devices do strange things. Security software sometimes does stranger things. I’ve seen all of that before. I filed the moment away in my head—not alarmed, but slightly crooked. Like a picture frame that isn’t hung quite right.
The next day, accounting mode continued. Numbers. Forms. Pressure to finish.
And then the unease returned.
I opened Autoruns and looked at what was set to run at boot.
There it was.
Something called “screen share.”
Generic name.
Generic folder.
Living quietly under C:\Program Files.
That was enough.
Not enough to panic.
Enough to stop.
Before doing anything else, I picked up the phone and called my larger customers.
I didn’t hedge. I didn’t soften it.
“I clicked on the wrong thing. My PC may have been under the control of someone I don’t know overnight. I didn’t realize it until a few hours ago.”
That sentence mattered more than any software decision.
My job wasn’t to be innocent.
My job was to protect others.
After the calls, I disconnected the machine entirely. Air‑gapped. Powered on, logged in, untouched. All my data still there—but isolated. Nothing leaving. Nothing spreading.
Here’s where timing stepped in.
On the other desk sat a clean, vanilla Windows 11 notebook. Fresh install. Different password. It had been serving a noble purpose—letting my son Dominik watch YouTube while we were still at the old house. He didn’t need it anymore. I’d be sleeping at the river house in a couple of days anyway.
It was just… there. Ready.
Earlier, I had already moved QuickBooks to a dedicated PC.
Earlier still, I had built a completely separate machine just to test a client VPN.
Not because of fear. Because of habit.
Segmentation. Blast radius. Least privilege.
The kind of boring preparation you only notice when it saves your day.
So I moved forward using the clean machine, transferring only what I needed, only when I needed it. Efficient. Calm. No scorched earth. No heroics.
Later—when I finally looked closely at the email that started it all—the truth was obvious.
The sender domain wasn’t Coinbase at all.
It was privately registered.
A Windows installer was attached.
Elegant. Precise. Perfectly timed.
Urgency was the real vulnerability.
That’s why I used to tell students in my security classes:
“I make mistakes too. And if something happens, tell us. Our job isn’t to blame. Our job is to restore.”
This wasn’t a story about getting hacked.
It was a story about noticing, about slowing down, about telling the truth before certainty.
And about discovering—at just the right moment—that enough had already been put in place.
You really can’t make this stuff up.